Confidently Secure Your Email With Symantec
Powerful protection: A leading email security solution with isolation technology
At Symantec, a division of Broadcom (NASDAQ: AVGO), we take your cyber security seriously, and we have long recognized that email is inarguably one of the most important threat vectors that organizations need to secure. Not only is 94% of malware delivered by email; email is also used to send links to websites that in turn host malware or phishing attacks. And the risk doesn’t stop here – Business Email Compromise and spoofing attacks are designed to bypass normal organizational controls, and email is a considerable risk factor that needs to be addressed as part of a data loss prevention strategy.
Since being acquired by Broadcom over half a year ago, we remain committed to developing our Email Security portfolio. Our investment in Email Security continues, not just in enhancing our core Email Security service, but also in extending the integrations and threat intelligence that supports this to provide ever stronger and high quality protection for customers. This is important to state as there are some organizations who would lead you to believe that this is not the case.
Customers, and industry analysts alike have recognized the strength that comes by Symantec offering a wide range of security technologies, and the underlying Threat Intelligence which it offers. If we consider the problem of web hosted malware and phishing attacks, I want to show you how our integrated approach keeps customers safe.
At Symantec we take your cyber security seriously, and we have long recognized that email is inarguably one of the most important threat vectors that organizations need to secure.
We know many of these attacks start with an email. We use a range of email validation, anti-spam and anti-malware filters to scan every email for signs that it is risky. This includes checking that the email isn’t impersonating or spoofing an email domain (for example “syrnantec” instead of “symantec”) and sender authentication standards have been complied with. We also scan for indicators of risk (e.g. language used in spam or fraud), embedded code in the email and attachments as well as examining any links. Advanced threats can also be sent to a sandbox for additional malware detection checks.
We cross check URL data with the threat intelligence from our web security platform, allowing us to use information such as the IP address range and lifespan and reputation scores for a website to determine the risk associated with that email. Because we know websites can ‘turn bad’ at any point, we use Real-time Link Following capabilities to scan links again when the user clicks the email, offering important protection and further reducing risk.
The reality is, that despite all these checks, there are still websites that cannot be categorized as being simply good or bad. There are always websites that remain risky, and these websites present a dilemma. Do you allow users to access those websites, with the risk of a breach? Or overblock website access leading to reduced productivity and frustration?
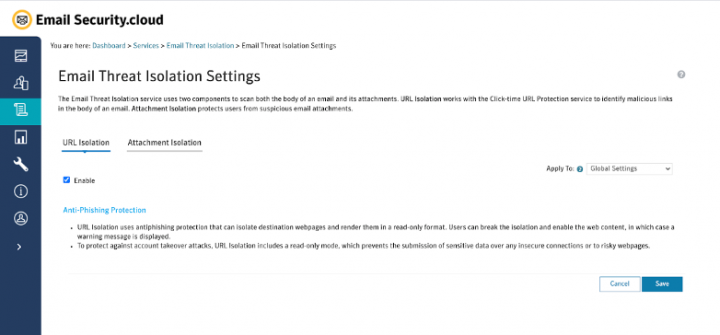
Symantec Email Threat Isolation resolves this in an incredibly effective, elegant, and simple way. A simple checkbox activates this protection – Symantec’s security experts control the policy for you.
Any risky or uncategorized website or email attachment is now opened in a secure, isolated web browser. The user has full access to the information, can navigate and interact as normal (with no noticeable impact on browsing experience) and is kept safe from malware attacks – there is no line of sight from the website to the user’s device. In addition, websites can be presented in read-only mode to prevent phishing attacks, no matter how authentic the fraudulent website appears.
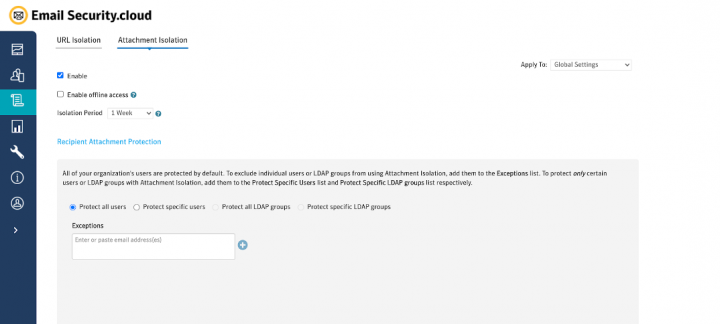
Similarly, risk email attachments allow the user to ensure the attachment is authentic before inadvertently allowing malicious code or scripts to execute on their device.
This is just one example of how our approach to Email Security is keeping customers safer. We believe our combination of leading email security coupled with world class threat intelligence and security integrations - such as Isolation - delivers better security outcomes, in a simpler to manage way.
Within our portfolio we have the ability to secure email in a number of ways. Whether customers need a physical or virtual messaging gateway, a cloud hosted service or a hybrid deployment we have the solution. Protecting against the myriad of threats facing organizations today requires multiple defenses. Different technologies are needed to stop spam, unwanted email, impersonation attacks, Business Email Compromise, infected email and attachments, risky web links, phishing attacks and data loss.
Symantec keeps customers safe by providing a set of capabilities that includes:
- sender authentication
- email body and attachment inspection
- URL link following
- behavioral analysis
- user awareness training
- advanced threat protection
- encryption
- data loss prevention
- website & attachment isolation
This breadth and strength of protection is recognized by industry analysts, independent test organizations and perhaps, most importantly, our customers. As we’ve reported in the past: both here and here, we’re proud to have been recognized by analysts in their recent reports. Both as a Leader in The Forrester Wave™: Enterprise Email Security, Q2 2019 report, as well as a Top Player in The Radicati Group's Secure Email Gateway - Market Quadrant 2019.
Find out more about the breadth of our full Email Security solution by visiting our website.

Once Again, Symantec Recognized as a Leader in Email Security
Symantec Named a Leader in Email Security by Third-Party Evaluators







We encourage you to share your thoughts on your favorite social platform.