The Ransomware Threat in 2021
New research from Symantec finds that organizations face an unprecedented level of danger from targeted ransomware attacks as the number of adversaries multiply alongside an increased sophistication in tactics.
For the last number of years, targeted ransomware has been one of the main cyber risks for businesses and other large organizations. However, as outlined in a new whitepaper from the Symantec Threat Hunter Team, a part of Broadcom Software, the past twelve months have seen ransomware attackers become more aggressive, finding more ways to increase the reach of their attacks, and becoming more ambitious by mounting a number of audacious and highly disruptive attacks.
The attack against Colonial Pipeline in the U.S. in May 2021 caused significant disruption and prompted concerns about the nation’s fuel supplies. In the same month, an attack on Ireland’s national health service, the Health Service Executive, forced it to cancel thousands of appointments and initiate a recovery operation that is only now concluding.
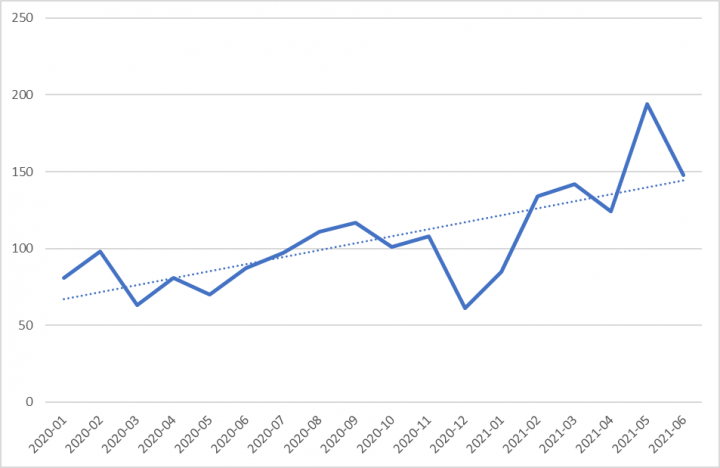
While the overall levels of ransomware activity have fallen, this is accounted for by the decline of mass-mailing, indiscriminate ransomware attacks. Of greater concern is that the number of organizations confirmed as affected by targeted ransomware attacks increased by up by 83% over the past 18 months, from 81 in January 2020 to 148 in June 2021.
The real number of targeted ransomware attacks is much higher. Confirmed attacks from known targeted ransomware families are probably only a representative sample of the overall number of attacks involving these threats. Many targeted ransomware attacks are halted before payload deployment, meaning they may not be identified as ransomware. In addition, most targeted ransomware operators recompile their ransomware for every new attack. This means that the variant of the ransomware used in an attack may be blocked by generic or machine learning-generated detections rather than a detection linked to that ransomware family.
Alongside this increase in activity levels, the ransomware threat landscape has become more complex and sophisticated and a number of new developments have compounded the threat for organizations.
The rise of ransomware-as-a-service
Although ransomware-as-a-service (RaaS) is not a new concept, the RaaS marketplace has evolved significantly over the past year. The basic template currently involves ransomware authors offering access to the ransomware itself, hosting for breached data, and handling of ransom negotiations. In some cases, it has been reported that ransomware developers provide an entire playbook for affiliates.
However, some ransomware affiliates now appear to be becoming less reliant on ransomware authors. While affiliates have long been known to migrate to other ransomware developers if the developer they were working with shuts down, many are now using their own distinct tools, tactics, and procedures (TTPs) regardless of the payload they are deploying. Some affiliates now appear to be simultaneously collaborating with more than one ransomware author. Symantec Threat Hunter Team has observed affiliates using two different strains of ransomware in a very short space of time and, in some cases, during the same attack.
Botnet collaboration
Over the past 12 months, secondary infections, usually via botnets, have become one of the most prevalent means of access for ransomware groups. Trojans that were once used for financial fraud, such as Trickbot, have recently been repurposed mainly as distribution channels for other malware, most notably ransomware.
In some cases, ransomware attackers already control the botnets, such as the Miner group (aka Wizard Spider), which owns the Trickbot botnet. Trickbot has been seen as a precursor to attacks by Ryuk, which is also attributed to Miner. Similarly, Hispid (aka Evil Corp) have leveraged their own Dridex botnet, which was originally built to mount financial attacks, to give them a means of delivering the ransomware to organizations.
Other actors have since attempted to replicate this attack pattern, seeking collaborations with established botnet operators. The most notable of these is the use of IcedID by at least one affiliate operator of the Conti ransomware.
Unprecedented threat
The profusion of groups carrying out targeted ransomware attacks combined with the evolution of the RaaS marketplace now means that targeted ransomware poses a grave threat to organizations. Although ransomware gangs have attracted significant government and law enforcement attention in recent months, multi-million dollar ransom payments mean that most threat actors remain undeterred.
Further Reading
For more information, read our whitepaper:








We encourage you to share your thoughts on your favorite social platform.