Browser-Based Cryptocurrency Mining Makes Unexpected Return from the Dead
Once thought of as dead, browser-based cryptocurrency mining makes an unlikely return, coming back to haunt websites and their visitors.
Browser-based cryptocurrency mining activity exploded in the last few months of 2017. After many years of deathly silence, the catalyst appears to be the launch of a new browser-based mining service in September by Coinhive. This service wraps everything up nicely in an easy-to-use package for website owners and has injected new life into an idea that was long thought of as dead and buried.
Highlights of this blog
- Browser-based cryptocurrency mining is not new; it's been around since at least 2011.
- A surge in the cryptocurrency market in 2017, as well as availability of coins that are mineable using home hardware and easy-to-use JavaScript APIs, has led to a torrent of malicious browser-based mining affecting many well-known and lesser-known websites.
- Mobile devices have not been spared from cryptocurrency mining, as witnessed by a 34 percent increase in the number of mobile apps incorporating cryptocurrency mining code.
Tried, tested, and buried
Browser-based mining, as its name suggests, is a method of cryptocurrency mining that happens inside a browser and is implemented using scripting language. This is different compared to the more widely known file-based cryptocurrency mining approach which involves downloading and running a dedicated executable file.
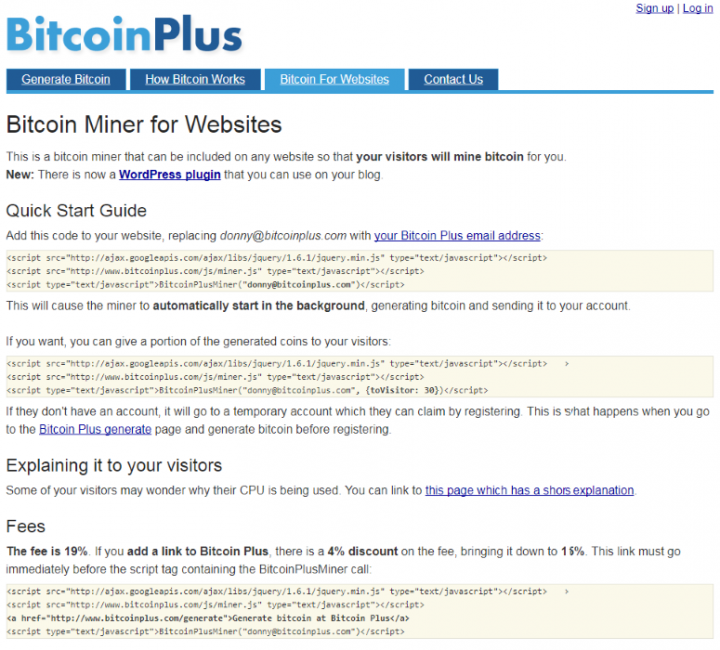
Browser-based mining dates back to May of 2011 when an innovative service called BitcoinPlus.com was initially launched—back when Bitcoin was cheap and mining was easy—not to be confused with another cryptocurrency known as Bitcoin Plus.org (XBC). That service was in many ways remarkably similar to its modern reincarnation, Coinhive. It used JavaScript code for pooled mining and website owners could sign up to the service and embed these scripts into their web pages to make page visitors mine for them. The big difference is that back in 2011 BitcoinPlus.com, as its name suggests, mined for Bitcoin (BTC) whereas the current browser-based miners like Coinhive are mining for Monero (XMR)—a newer, privacy-focused cryptocurrency. Back in 2011, before the advent of ASIC mining in 2013, Bitcoin was still in its infancy, mining difficulty was relatively low, and cryptocurrency prices were even lower. It was (just about) possible to do some mining with home-grade hardware.
Even though it was possible at that time to mine for Bitcoin via BitcoinPlus.com, the reality of the situation was that it was largely a futile exercise. The reward was minuscule compared to the amount of mining power and electricity required. Of course, this was back in the days before Bitcoin prices shot through the roof—in June 2011, Bitcoin reached the then lofty heights of almost US$30.
Due to this fundamental profitability problem with browser-based mining, it soon withered away. However, the idea was once again revived in December 2013 by a group of MIT students in a project called Tidbit—ostensibly touted as an alternative way for website owners to raise revenue. Once again, this project didn’t last long, as soon after it started the New Jersey Division of Consumer Affairs stepped in to investigate the fledgling company on charges of unlawful access to "a person’s computer processing power." This resulted in a long drawn out case which was finally settled in 2015.
The case for browser-based mining wasn’t looking good. The growing problem of profitability was made even worse by the increasing use of ASIC miners. The advent of ASIC miners dragged bitcoin mining out of the realm of home users and into an industrial age dominated by the massive mining farms that we are more familiar with today. After the demise of Tidbit, the idea of browser-based JavaScript cryptocurrency mining largely died away once again.
Despite these setbacks, key lessons were learned. The point of a service like Tidbit was never about single servers or high-end computers doing solo mining. The true power of this service came from scaling up and pooling the potentially massive combined mining power of masses of users with average hardware visiting a website. Higher website traffic means higher returns and sooner or later, somebody was bound to figure out a better way to get browser mining to work on end users' computers more efficiently.
Dawn of the dead
Fast forward to September 2017, the cryptocurrency landscape compared with 2013 had changed drastically. In April 2013, the cryptocurrency market only had a handful of coins and the total market capitalization was just $1.5 billion. The market for cryptocurrency was extremely limited and illiquid, meaning that even if you got some, it was not easy to turn it back into fiat currency for spending. Contrast that with September 2017 when the market capitalization stood at an incredible $166 billion spread over more than a thousand different coins.
Together with the diversity of coins to choose from in 2017, there was also now a diversity of coin reward mechanisms. Some, like Bitcoin, can still only be mined via a proof-of-work (PoW) process using dedicated power-hungry ASIC hardware—though there have been attempts to change this, with the various hard forks such as Bitcoin Gold (BTG) and Bitcoin Diamond (BCD), to bring in GPU mining. Other cryptocurrencies like Monero, Ethereum (ETH), Ethereum Classic (ETC), and Dash (DASH) can be mined using retail-grade GPU hardware found in many home computers. There are also some that are more suited to CPU mining; these include Monero and Verium Reserve (VRM). The trading environment is massively different too; it’s now much easier to move between fiat currencies and cryptocurrencies, making the latter more useful and valuable.
It's against this backdrop that Coinhive released its browser-mining scripts designed to mine Monero, effectively bringing the idea of browser-based mining back from the dead.
News spreads fast
Coinhive is marketed as an alternative to browser ad revenue. The motivation behind this is simple: users pay for the content indirectly by coin mining when they visit the site and website owners don't have to bother users with sites laden with ads, trackers, and all the associated paraphernalia being downloaded to the browser. Users hopefully then get a cleaner, faster, and potentially less risky website (remember malvertising?) to use, and everybody is happy. What could go wrong?
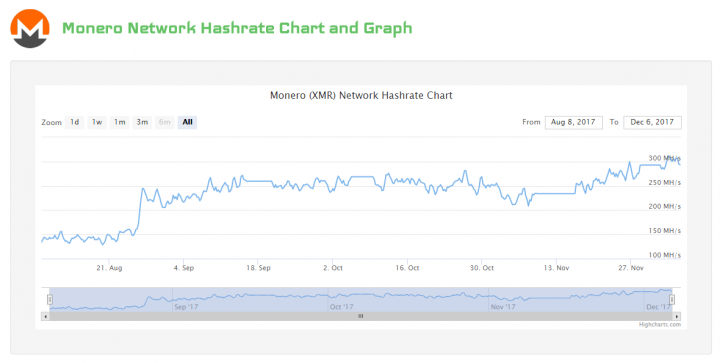
Soon after the release of the Coinhive service, the hash rate for the service started to climb, and quickly too. Hash rate is the number of hashes calculated by the combined power of the mining pool and is measured in the number of hashes per second—usually in units of millions (MH/s). Hashing is the process of carrying out cryptographic hash calculations which are used to help process transactions. Miners who participate in a mining pool get paid a share of income generated by the pool.
According to a blog by Coinhive, the hash rate for their pool climbed from 0 MH/s to 3 MH/s in a couple of days before reaching 13.5 MH/s in the space of a week. To put that into perspective, the total network hash rate (the total amount of mining power for all computers mining) for Monero stood at around 260 MH/s on September 20, 2017. The Coinhive pool reached just over five percent of that total which is quite an achievement in such a short time.
Monero can be mined with CPUs and GPUs, but the Coinhive browser-based mining service only works for CPU mining which is a limitation that substantially reduces potential returns.
To maximize revenue, the script is best placed on high-traffic websites and "sticky" websites (where users stay on the same page for longer). According to one early adopter, the revenue generated by his particular site was far lower than the revenue generated from ads.
In fairness to Coinhive, it recommends being transparent with site visitors and that website owners notify users of the mining that will be taking place and, better still, offer users a way to opt in. Unfortunately, despite Coinhive’s best intentions, unscrupulous operators quickly latched on to the idea of secret mining in the hope that users will not notice.
Start of a torrent
The first high-profile site to start using Coinhive mining was The Pirate Bay torrent website. The Pirate Bay has had a checkered history and, being a highly trafficked site (global ranking #161 with 290 million visitors in the last six months), has been looking for alternative ways to monetize its considerable traffic. Its initial attempts at browser mining were quickly spotted by users and they were not too happy about it. At least in the case of The Pirate Bay, this was a case of the site's owners making a decision to use Coinhive.
The Pirate Bay's initial attempts at browser mining were quickly spotted by users and they were not too happy about it.
The Pirate Bay was soon followed by another high-profile site—this time Coinhive's miner was found on two of Showtime's websites. One of the Showtime sites affected was its content streaming site which has high traffic and user sessions are lengthy as visitors stay on the site while content is streaming. Showtime is a premium-based service so it would seem strange that users are made to pay twice for content. The scripts were promptly removed after they were discovered, suggesting that they were planted there maliciously.
Reports of many other sites using the Coinhive mining scripts soon followed. Over the Thanksgiving holiday in the U.S., the Coinhive miner was also found in a LiveHelpNow widget which is used by many websites around the world to offer in-browser support chat sessions. The apparent cause of this was the compromise of one of the CDN servers used by LiveHelpNow to serve up its widget. As with Showtime, LiveHelpNow is already a legitimate revenue-generating business and there's no obvious reason as to why it would risk user confidence to earn a few extra bucks from users. So the most likely scenario is that the server was compromised either by an outsider, or even an insider.
Browser mining is cropping up in many other different places too:
- Browser extensions and plugins have already been found with browser-mining scripts.
- Even the traditional tech support scam pages are incorporating browser miners into their pages as an additional revenue stream. The heavy CPU use caused by mining may actually help convince the user that they have a problem and may increase the chances of users falling for the scam.
- People have even been trying browser mining on parked domains—these are the kind of websites that you can sometimes end up on when you inadvertently misspell a domain name.
Why is browser mining taking off?
There are many reasons why browser-based mining is back with a vengeance. Unlike in previous failed attempts, recent developments in the cryptocurrency and threat landscapes have made this a much more viable activity. Let's have a look at some of these factors in more detail:
Advent of privacy-focused cryptocurrencies
Privacy is important if you want to mine coins maliciously, in order to ensure others cannot easily follow the money trail back to you. Monero, which came to the market in 2014, can offer a high level of transaction privacy. Unlike with most other cryptocurrencies that use public transparent blockchains where transaction addresses can be easily viewed by anyone, Monero does things differently. By default, everything is private, including the amount in a transaction, who sent it, and who received it. There is an option with which wallet owners can selectively reveal some information via what's called a view key, but this is not a feature that cyber criminals are likely to want to use.
Ease of use
As mentioned earlier, Coinhive provides a very neat and easy-to-use package for people to get involved in Monero mining. All you have to do is add a few lines of script to your website code. You don't have to make website visitors download and install executable files.

The mining process can start quickly and quietly in the browser without anybody noticing, unless insufficient throttling is used, in which case the CPU load may max out during the users' session which would be an easy tell-tale for end users to spot.
CPU load may max out during the users' session which would be an easy tell-tale for end users to spot.
Profitable to mine with common home hardware, at scale
Even with the price of Monero reaching over $300 recently, given the current network hash power of the network at around 300 MH/s, profitable mining is a game of scale and requires a careful eye on costs.
With browser-based mining, the cost of mining is borne mostly by the website visitors through hardware wear and tear as well as energy costs. Scale is achieved by using high-traffic sites with sticky content.
Coinhive currently pays 0.000104 XMR ($0.025) for every million hashes. Take for example a user of a PC with a mid-range Intel i7-7700K CPU which is capable of pushing out around 300 H/s. The user would have to spend 3,333 seconds on the site, or roughly 55 minutes, in order to achieve a million hashes. However, if you can get 3,333 users to spend approximately one second each on the site it would achieve a similar result.
Even under optimal conditions, the amount of hashes produced in each instance will be small, but when it comes to distributed computing power, it's all about scale and every little bit adds up.
The cryptocurrency growth factor
As we noted earlier, the value of mining rewards are not great, at least not initially. To get a better understanding, we need to look at the profitability of this activity over the longer term and take in the macroeconomic picture to get a true sense of the reward. The value of cryptocurrencies like Monero is going up dramatically. So far in 2017, the price has gone from $13 to over $300. Under these circumstances where the price of Monero can go up substantially in dollar terms over a relatively short time, mining Monero can become an attractive proposition. A small amount of Monero mined today could potentially be worth a great deal more in a matter of months (conversely it could also drop significantly depending on the health of the overall cryptocurrency economy).
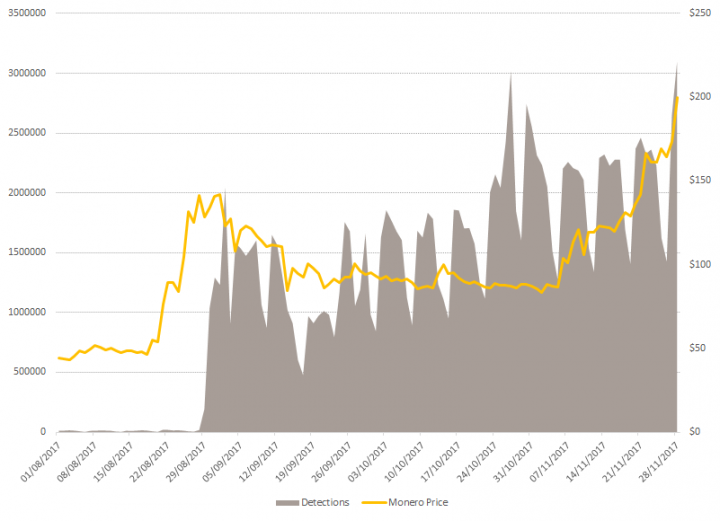
Mirroring the rising interest and price of cryptocurrency, we have also seen a big jump in our detections of both file- and browser-based cryptocurrency mining activity in recent months.
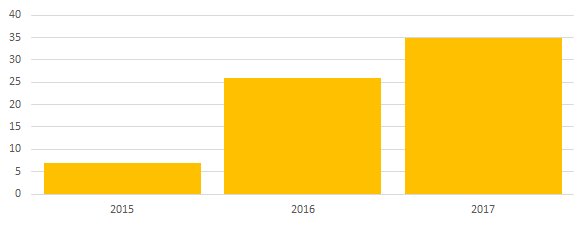
Mining on the go
Malicious cryptocurrency mining isn't just confined to desktop computers and servers. Always-connected mobile devices are also a growing target. We have even seen growth in coin mining on mobile phones in recent years. In 2016, we discovered 26 different Android apps that were mining cryptocurrencies. So far in 2017 we have found 35, which is around a 34 percent increase.
Modern mobile phones have processors that can be as powerful as low- to mid-range desktop computers which help to make mobile mining more viable. But cryptocurrency mining is always an energy-intensive activity so the biggest problem facing mobile mining is of course battery drain as battery technology has not progressed as fast as processing power. Mobile mining will inevitably be noticed by the heat generated and the fast-draining battery, not to mention any performance impacts that it may also have on the device.
What does the future hold?
If we consider the cryptocurrency market as whole, we can see that just as the total value of cryptocurrencies increased manifold during the year, interest in malicious mining activity, both browser- and executable-based as indicated by detections of malicious mining activity, increased in tandem with it.
As interest increases, more participants, both as miners and tool makers, join the fray. Coinhive, while being the best known at this time, doesn't have the market to itself. Similar projects like Crypto Loot are cropping up, and other browser mining projects like JSEcoin have been in beta since August 2017 and are trying to generate growth in this activity.
Symantec has observed a significant jump in all cryptocurrency mining activity in recent months as evidenced in our increasing detection rate (See Figures 4 and 5). Despite the genuine aspirations of most browser mining projects to offer a real and potentially better alternative to traditional web revenue generation methods, the sad reality is, it can and is being misused.
Increasing user awareness and detection by security vendors will trigger a new arms race between cyber criminals and defenders. Recent innovations in the malicious use of browser-based mining scripts, such as the "pop-under" technique where browser mining takes place in a hidden browser window, are a sign of this in action. We can expect to see adoption of a wide range of traditional malware propagation and evasion techniques to help spread and prolong mining activity in order to maximize profit. For as long as the current enabling factors are in place making it favorable for mining, we can expect to see interest in browser mining to be sustained or even increase in the short to medium term.
How Symantec helps prevent browser mining
Symantec is keeping a watchful eye on the growing trend of browser mining. We are making adjustments as necessary to prevent unwanted cryptocurrency miners from stealing your computing resources to enrich others.
Website owners should watch for injection of the browser-mining scripts into their website source code. Our network solutions can help you spot this in the network traffic as your server communicates with visitors. In addition, file system scans can also show up any files where the browser-based miner code has been injected, enabling you to identify and clean up the content.
Symantec helps prevent others from stealing your computing resources by protecting various stages of the attack chain:
Blocking network traffic associated with browser-mining activity
All mining software, whether it is file- or browser-based, must be able to connect to either the cryptocurrency network or a mining pool to exchange data, in other words its proof-of-work. Without this connection, it cannot get the data it needs to generate hashes, rendering it useless. We can also block the mining scripts from being downloaded in the first instance. Our network protection operates on our endpoint solutions as well as our gateway and cloud touch points; all these solutions help build a solid defense against unwanted mining activity.
Here are some of the network protection signatures geared towards detection of browser-based mining:
- Web Attack: PUA.JSCoinminer Download
- Web Attack: JSCoinminer Download
- Web Attack: JSCoinminer Download 6
- Web Attack: JSCoinminer Download 7
- Web Attack: JSCoinminer Download 8
- Web Attack: JSCoinminer Download 10
- Web Attack: JSCoinminer Download 12
- Web Attack: JSCoinminer Download 13
- Web Attack: JSCoinminer Download 14
- Audit: JSCoinminer Download 3
Blocking browser mining activity on endpoints
Our endpoint solutions, including those for mobile devices, can detect and block all types of mining activity whether they are file-based or in-browser. These solutions can prevent mining software from installing or running in the first instance. Browser-based mining scripts are detected as PUA.JScoinminer.








We encourage you to share your thoughts on your favorite social platform.