Why CASB is the Perfect Home for Cloud Security Posture Management
Vendor consolidation, integrations, differentiation and silo elimination in one neat offering
Human Error - The Bane
If you were to ask a colleague to set up a cloud workload, while they were under pressure, it’s fair to assume a mistake may be made. If that mistake led to a cloud misconfiguration, the consequences leading to a data breach are easy to imagine. Several high-profile breaches due to misconfigurations have proved that we ought to:
“Learn from the mistakes of others. You can’t live long enough to make them all yourself.” - Eleanor Roosevelt.
Roosevelt offers very sage advice particularly for Cloud Security. Learning from the mistakes of others is important because making them yourself could mean loss of business, customer trust, reputation damage, and exorbitant legal costs.
Human error leading to misconfigurations and inadvertent mistakes are the leading cause of data breaches, reported or not. The question to ask is why is human error still an issue even with the evolution and maturity of IT and security operations over decades?
The answer is scale, ready availability, and unbounded two-way accessibility combined with the “time-to-market” pressures that businesses face in today’s competitively cut-throat environment.
- Scale is often mind-boggling and overwhelming to the human mind. Combine it with computing resources on-tap, and you have a sure-fire recipe for disaster. Self-provisioning, speed, agility, and the scale of the cloud takes no time in transforming itself into Frankenstein’s monster, if not handled properly.
- Ready availability refers to the self-provisioning nature of cloud platforms. There are other pitfalls of self-provisioning, such as surprise or uncontrolled costs. However, from a security standpoint, the risk of mistakes, misconfigurations, and misjudgments—undermining the downstream impact of a callously ignored setting—are far greater than the cost issue.
- Accessibility not only from within the corporate network to the cloud but also from the outside in. An innocent unintended misconfiguration provides the attacker a foothold in the network. This can make way for easy initial access, unbridled lateral movement, and sometimes, with a stroke of serendipity, direct access to the data depending on the type of misconfiguration.
- Time to market - the pressure-to-ship faster and more often means that developers are more likely to leave default settings in place, or ignore security warnings by cloud providers.
CSPM - The Answer
After multiple high-profile exposures/breaches—some of who became the poster-children of breaches due to misconfigurations—SaaS-delivered Cloud Security Posture Management (CSPM) products began making an appearance on the global cybersecurity scene circa 2018. The industry responded with equal fervor and soon enough, there was an exponential increase in the number of CSPM vendors. Symantec, by Broadcom Software, truly demonstrating its thought leadership, developed CSPM organically which came to be known as Cloud Workload Assurance (CWA). However, as the CSPM market became more crowded and newer cloud security use cases emerged, customers realized that managing multiple, siloed security solutions presented its own problems—the so-called “swivel-chair security” problem where you have to constantly shift attention and risk missing the big-picture view.
Integrated CSPM, CASB, DLP - The Solution
As the vendor consolidation theme continues to dominate customer conversations, Symantec, by Broadcom Software, has doubled down on an “integrated solutions” approach over solving isolated use cases. Tackling security use cases with a one-for-one approach leads to security gaps with patchy and unwieldy risk management.
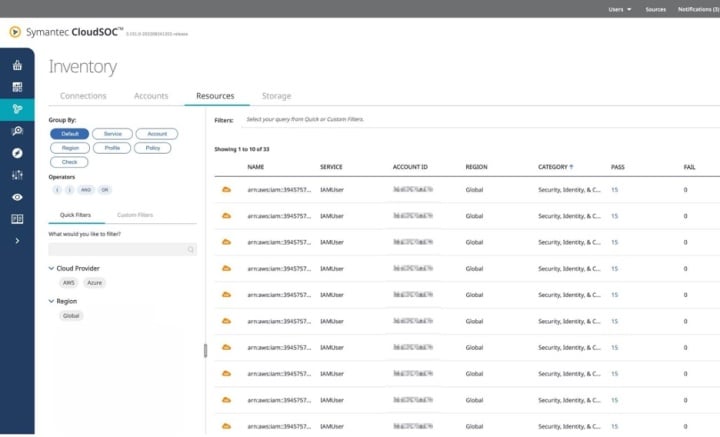
As a part of this broader initiative which involves bringing all of the Symantec security products together to deliver coherent and consistent security outcomes, CWA has found a new home in CloudSOC (CASB).
Another benefit of having CSPM available with Symantec’s award-winning DLP and CASB is that you don’t have to worry about onboarding your cloud accounts or creating connections over and over to monitor and protect them.
Further, the integration provides granular visibility and control over users, data, applications, and configurations - all of which is a customer’s responsibility according to the Shared Responsibility tenets laid down by Cloud Service Providers (CSPs).
Good-bye, swivel-chair security!
To learn more, contact your Broadcom Software sales representative for more information. Alternatively, why not attend one of our regular User Groups? More information is available here.

Tolly Group Validates Symantec Product Alignment with SASE
Offering our customers so much more







We encourage you to share your thoughts on your favorite social platform.