Symantec XDR: Data Normalization is the Key
Normalization Allows for Correlation and Richer Threat Intelligence
To provide your organization an effective cyber defense, you need to see clearly what’s going on. That means gaining a broad view of all control points – no easy task when many companies have deployed a multitude of disparate security technologies. Unless the events from these security tools can be coalesced, cyber security personnel can be easily overwhelmed, leaving their organizations vulnerable to attack.
At Symantec, a division of Broadcom (NASDAQ: AVGO), Extended Detection and Response (XDR) is our strategy for simplifying and uniting cyber security tools, as Ryan Stolte, CTO of our Information Security Group, explains in this blog entry. Thanks to XDR, when an incident happens, you can identify it across all control points – network, email, cloud, identity, information and endpoint. That enables you to tell how malware got in, how long it stayed and what it did. That seems straightforward, but how does it work? Let’s take a look under the covers.
To provide your organization an effective cyber defense, you need to see clearly what’s going on.
The first step is to collect information across all the control points, starting with logging information. Again, it sounds simple. But cyber security tools log events differently, using different nomenclature. A destination IP address, for example, might be expressed one way by one tool and another way by another.
The solution to this is data normalization. It’s far from a new idea, but data normalization is especially necessary in this context. When you bring together lots of data from different sources in a data lake for use by an analytics platform, you have to make sure the data from each control point is labeled in a consistent way.
ICDx makes it work
That’s where Integraterd Cyber Defense Exchange (ICDx) comes in. Built-in ICDx collectors gather log information and put it into a data schema so that username, IP address, role and process are labeled consistently across all the different control points. This normalized data provides a contextual, visual picture to help the analyst perform triage, incident response and incident remediation. Without the data normalization capabilities of ICDx, a SOC analyst is faced with unwieldy manual processes.
As you can see in the diagram below, ICDx sits between numerous data sources (at the top) the SOC and SOC front-ends (at the bottom).
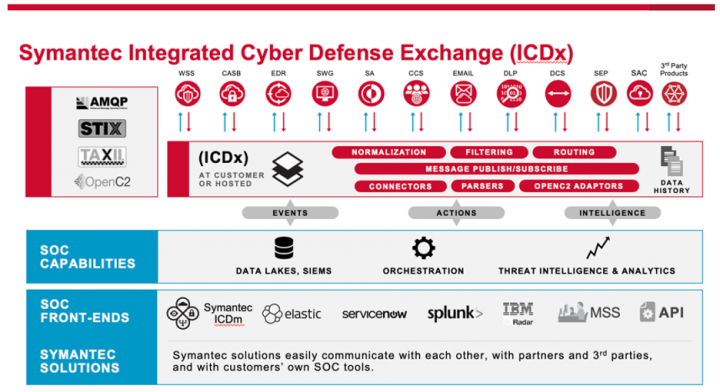
In addition to data collection and normalization, ICDx includes these capabilities:
- Smart forwarding: enables a manager to define the parts of log events that should be sent to different destinations. For example, threat information might be sent to a SIEM, while log information might be forwarded to a data lake. Meanwhile, all logs can be sent to a centralized archive for compliance.
- Automated response actions: enables an analyst to block a file across the enterprise. ICDx federates the blocking action and applies it across all control points.
- Analytics: enriches data with threat intelligence, then feeds it to a SOC front end.
- Third-party integration: provides interoperability with multivendor products. Integration through Open IOC enables an analyst to search for indicators across Symantec and non-Symantec products.
In short, ICDx is the integration and routing point of XDR. Considering the number of tasks it performs and the complexity it simplifies, it’s remarkable that configuration requirements of ICDx are minimal: All you need is IP address, username and password. Then just press a button. Soon your control point data will be normalized and you’ll gain the complete enterprise view you need to provide the cyber protection your organization deserves.
Here’s where to find out more and download ICDx for free: go now

Symantec XDR: A Streamlined Approach to Enterprise Security
Simplifying Enterprise Security Architecture









We encourage you to share your thoughts on your favorite social platform.