How Cyber Security is Changing in the Post-Pandemic Era
Broadcom Software suggests cyber security is a MUST for every enterprise
The last few years have been anything but normal for everyone. As we know at Broadcom Software, even as enterprises try to put a couple of abnormal years in their rear-view mirror, the rampage of ransomware continues to wreak havoc and requires continued focus and diligence.
The ransomware threat now dominates every security discussion I have with customers. Their concerns are justified: ransomware gangs are more sophisticated, determined and eager than ever to extract huge ransom payments. They are also deploying surprisingly creative tactics. Gone are the days of merely encrypting or stealing files – now the bad guys are leaking stolen information to put added pressure on their victims.
The goal: a BIG payout. For example, one ransomware gang publicly disclosed a CEO’s affair, complete with incriminating pictures. Another gang auctioned off company files to the highest bidder, with CNA Financial Corp. reportedly paying out $40 million to regain control of its network.
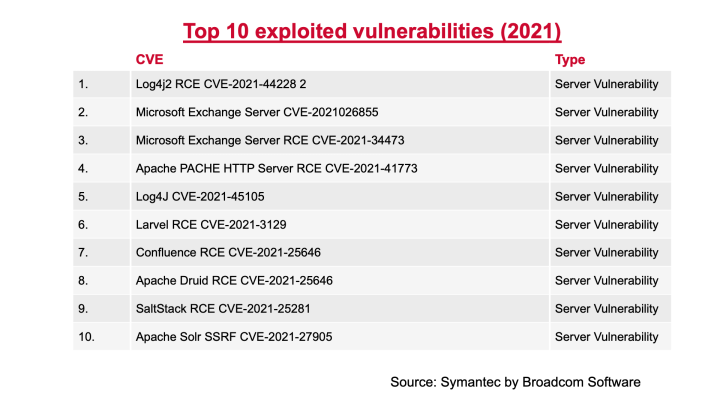
Meanwhile attackers are using different techniques to penetrate enterprise networks. In the last year, there’s been a pronounced shift to mass scans of the Internet to search out published server vulnerabilities as a way to get into enterprise environments. That’s partly in response to software vulnerabilities released in those servers. But it’s also an important reminder that attackers are relentless in their pursuit of new and softer targets.
They also are working harder to evade defensive measures when they get onto an endpoint. Traditionally, attackers would just drop their malware on the endpoint and run it. Recently, we came across a case where the attackers had installed a virtual box onto the endpoint and then downloaded a disk image. When the virtual machine started, the malware was loaded only inside of the virtual machine. The virtual machine had shared folders with the host so when the ransomware ran inside of the virtual machine, it was able to encrypt files.
When attackers penetrate an enterprise defense, they now recognize that they no longer have to encrypt every machine on a network. Instead of encrypting 10,000 computers, they can opt to take over the domain controller, the ESX servers and the virtual machines and encrypt the virtual machines’ images. This strategy has paid off for the bad guys as more than a few enterprises have been willing to pay ransoms to regain control and avoid the hassle of reimaging all their machines.
Choosing Their Victims
Over the years, the attacker underground has changed how it approaches target selection. In the past, we saw far more indiscriminate targeting – basically gangs went after anybody they could in a bid to find their way into enterprises.
In the post-pandemic era, attackers are more closely evaluating their targets to calculate the return on their time. So they’re investigating how much a company is worth? Is it listed on the stock market? How much cash do they have on hand? Essentially, this advance scouting work informs who makes the list and helps determine the size of the ransom attackers will demand from victims.
Trans-national Threats
As businesses look to shore up their defenses, they should know who they are up against. While ransomware attacks may come from anywhere, both security companies and government agencies have found evidence linking many attacks back to Russia.
The nature of the relationships between these ransomware gangs and the Russian government is opaque, but the persistence of the activity suggests, at a minimum, an indifference by the government to the impacts on the critical infrastructure and key industries of other countries or, at worst, direct government complicity if not sponsorship, but with a measure of deniability.
Even before the Ukraine invasion, Western nations had little luck convincing Russian authorities to crack down on ransomware gangs operating within its jurisdiction. Now, there’s even less chance of real progress.
Regaining Your Data
Once an attack takes place, options are limited. Ransomware crews have a secure encryption mechanism that security companies can’t break. So, when a business falls victim, it faces an impossible decision: shut down or pay? Often, management judges that it’s in the best interests of the company to accede. But there’s no guarantee the attackers won’t return a month later and ransom their data again.
If an organization is lucky enough to isolate the ransomware, it can restore its systems using offline backups that the ransomware crew didn't delete or corrupt. But even with backups, the process of restoring data is cumbersome and time consuming. Some organizations may conclude it’s preferable to pay the ransom.
C-level Support
If you’re looking for a ray of sunshine, it’s this: cyber security is now part of the C-level conversation. That wasn’t necessarily the case prior to the pandemic, although high-profile hacks in recent years have underscored the potential damage to a company’s reputation and bottom-line.
There’s no shortage of worst-case scenarios. To consider just one example, Colonial Pipeline Co., which operated the biggest fuel pipeline in the U.S., suffered a six-day shutdown last year after an attack by the Russian ransomware gang - Darkside. The upshot: higher prices, gas stations without fuel and criticism of the company’s pipeline security standards after the hack.
That’s why cyber security’s no longer a tough sell when the CISO presents to the boardroom. If in previous years cyber security was viewed skeptically as a big cost, it’s now seen as money well spent. Even if ransomware ultimately retreats, we’ve passed a digital Rubicon when it comes to how security is funded and prioritized within the corporate world.
Contact us here to learn more about how Broadcom Software can help you with your cyber security strategy.

Broadcom Software is Helping Lead the Way
The improving landscape of global cyber standards








We encourage you to share your thoughts on your favorite social platform.